Bloomberg Technology
How to Keep Your Brokerage Account Safe From Hackers
Oct.15 — Some Robinhood customers say their money was looted, suggesting online stock trading may be less secure than investors hoped. Experts share advice on how to protect yourself.
Bloomberg Technology
Tech Stocks Rally on the Back of US-Iran Ceasefire Deal | Bloomberg Tech 4/8/2026
Bloomberg’s Caroline Hyde and Ed Ludlow discuss the rally in tech stocks and fall in energy prices as markets react to a two-week ceasefire deal between the US and Iran. Plus, Anthropic is giving tech firms early access to its new Mythos model to get ahead of possible cyberattacks that could wreak havoc. And, Apple’s…
Bloomberg Technology
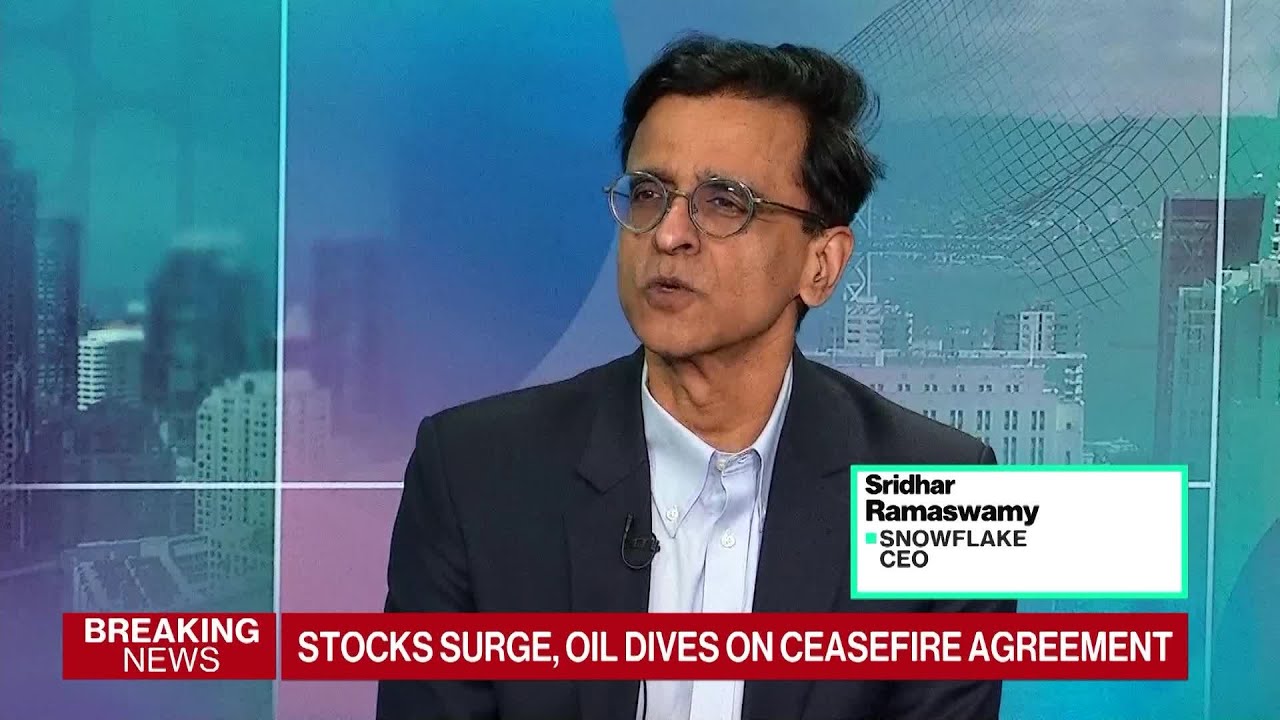
Snowflake Seeing Strong Return on AI Investment: CEO
Some of Snowflake’s coders are producing work 24 hours a day using AI agents, says CEO Sridhar Ramaswamy. He joins Caroline Hyde and Ed Ludlow on “Bloomberg Tech.” ——– Like this video? Subscribe to Bloomberg Technology on YouTube: Watch the latest full episodes of “Bloomberg Technology” with Caroline Hyde and Ed Ludlow here: …
Bloomberg Technology
Apple’s Foldable Phone On Track for September Launch
Apple’s first foldable phone is still on track to launch in September, despite reports of major manufacturing delays. Bloomberg’s Mark Gurman discusses the phone’s features and why it could mark a big shift in the foldable market. He joins Caroline Hyde and Ed Ludlow on “Bloomberg Tech.” ——– Like this video? Subscribe to Bloomberg Technology…
-

 Science & Technology6 years ago
Science & Technology6 years agoNitya Subramanian: Products and Protocol
-

 People & Blogs4 years ago
People & Blogs4 years agoSleep Expert Answers Questions From Twitter ???? | Tech Support | WIRED
-
 CNET6 years ago
CNET6 years agoWays you can help Black Lives Matter movement (links, orgs, and more) ????????
-

 Wired7 years ago
Wired7 years agoHow This Guy Became a World Champion Boomerang Thrower | WIRED
-

 Wired7 years ago
Wired7 years agoNeuroscientist Explains ASMR’s Effects on the Brain & The Body | WIRED
-

 Wired7 years ago
Wired7 years agoWhy It’s Almost Impossible to Solve a Rubik’s Cube in Under 3 Seconds | WIRED
-
 Wired7 years ago
Wired7 years agoFormer FBI Agent Explains How to Read Body Language | Tradecraft | WIRED
-

 CNET6 years ago
CNET6 years agoSurface Pro 7 review: Hello, old friend ????
















skyak
October 15, 2020 at 5:36 pm
Multi-factor authentication is a must but cellphones #s and email have been compromised in the past. Using tokens is cumbersome but worthwhile because it takes the security perimeter from worldwide to the actual physical token. Phones can act as tokens but then you have a single point failure from a stolen phone. Creating a VPN on your home network is advisable if you want to use public wifi.
Дима Фенаев
October 15, 2020 at 5:59 pm
0:53
activedating4.online